I’m running a website that is getting a lot of bot traffic and found Cloudflare free rule tier to be a bit limiting. (5 custom rules with length limits)
Ive got subnets for major VPS providers to block and will run analysis against my traffic to build on these lists.
What do others do?
I’m contemplating my Cloudflared tunnel into Crowdsec to my app.
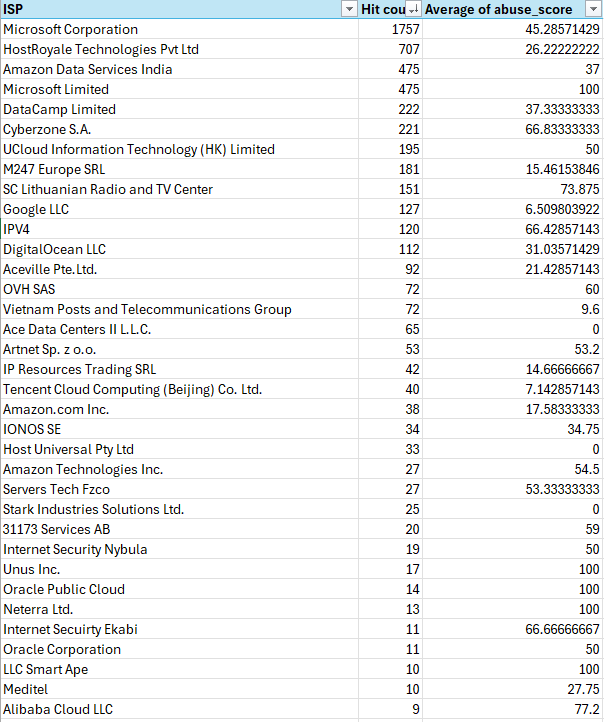
Edit: Adding in image of my analysis of the IPs scanning for vulnerabilities.

Wafs don’t make you safer but create unnecessary attack surface. Just keep your machine and services up to date.
You will need to explain a bit further this statement to mild knowledged internet stranger…
Because the point of waf is exactly about reducing the exposed surface…
Attack surface is made of the amount of code that is running when an attacker speaks to your machine. Imagine a freshly installed GNU/Linux distro with no services. The attack surface is minimal. All packages sent to your machine will only ever be touched by relatively limited parts of the linux TCP/IP stack and NIC driver. If you now run a web server, the package coes through the NIC driver, TCP/IP stack and web server. The surface is increased. Each of these parts of your machine’s code could have bugs. The more code your attacker’s packet runs through, the more opportunity to make your machine do things you don’t like.
If you want your machine to do what you like but not what random attackers like, it is therefore mandatory to have the least amount of attack surface, not adding code in contact with your attacker like a WAF or “antivirus”. Both these kind of softwares will inspect the packages coming in an take decisions (potentially bad ones) based on the content.
WAFs will mostly not help you since on a well configured and patched system, little known bugs are exposed. They might help you occasionally but usually patching the system is more effective. Of you want this to happen automatically, it’s entirely possible. Most os’s allow automatic unattended upgrades.
I’m trying to block the most likely attack vectors which is definitely VPS providers at this point in time. I just figure if I am blocking subnets plus additionals I identify it will force them out of these vectors to attack in ways I might be able to report better abuse.
Here check out my analysis.
Just don’t run broken software. The attackers will not be able to exploit you then. If they have zero day exploits, the WAF will most of the time not save you since they are often pretty easy to circumvent. WAFs are only effective against old and shitty exploits that should be patched anyways since ages.
I’d rather not have them probing my website at all. I’m not Facebook, my data is not unlimited and free.