Hybrid hard drive. Basically, a hard drive with a large solid state cache.
- 0 Posts
- 27 Comments
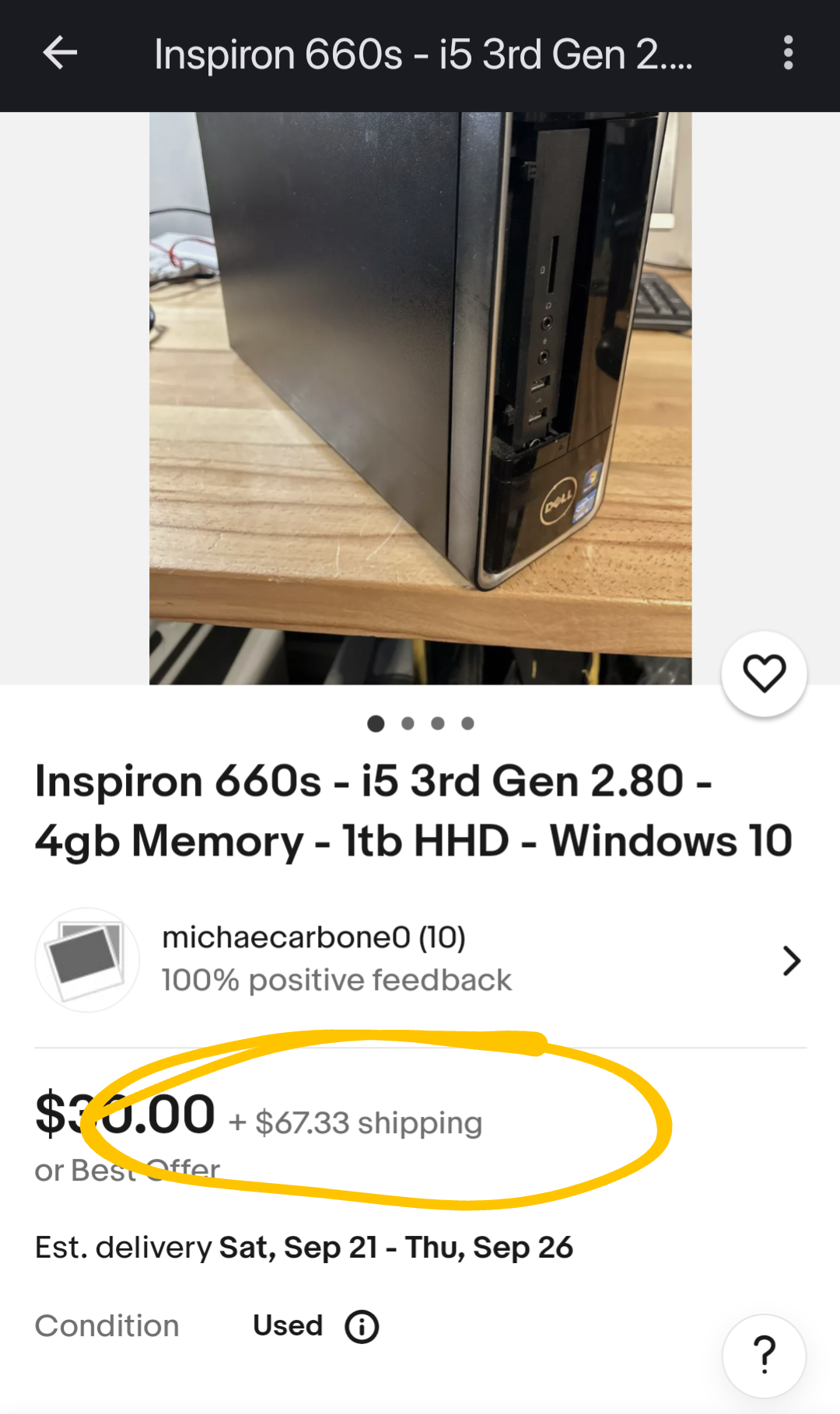
Actual shipping would vary depending on location, but sellers are padding the shipping charge so they can display a lower unit price.
Need to add shipping charges to the price…

 2·3 months ago
2·3 months agoI’m gonna go ahead and credit God with the sins of His followers.

 8·3 months ago
8·3 months agoWow.
That’s… Awesome.
Edit: That has pretty much every major feature I’ve been looking for.

 10·3 months ago
10·3 months agoLong shot, but does anyone know of any mapping app where you can easily project a bearing/azimuth line, or a point a given bearing and distance from another point?
The only app I’ve found so far that can come close to what I need is Backcountry Navigator, which has a terrible UI. Everything else seems to be focused entirely on GPS navigation from where you are now to a known destination; I have yet to find one that allows even basic triangulation, to be able to identify the location of an observed object.

 3·3 months ago
3·3 months agoDual boot sucks donkey balls.
Install virtualbox and spin up a Windows VM on a Linux host.

 285·3 months ago
285·3 months agoFuck all that.
Install Linux, any flavor. Install virtualbox, and set up a Windows VM. Go ahead and install any of your windows bullshit on that VM. That’s your crutch, your failsafe: a windows instance that you don’t have to leave Linux to access.
Save snapshots before and after any changes, so if/when it goes to shit, you can roll it back to where it was still working.

 3·4 months ago
3·4 months agoMy first thought (which probably isn’t the best method, but I’ve done similar before) is an Arduino between the mouse and the system. The Arduino normally just passes the mouse commands to the system, but it listens for the button and blocks movement if it sees the button press.
Because it’s all done in hardware, this method would be system-agnostic. You could plug it into anything.
I used a Teensy 3.6 for a similar project.

 4·5 months ago
4·5 months agoNeither of those options is particularly appealing to me. I’d look at building a more respectable file server, with 4 or more SATA ports. I’d have a relatively tiny SSD to host the OS, and any number of HDDs in some variety of RAID array

 3·5 months ago
3·5 months agoSSDs are fast; HDDs are slow. I would not want my operating system hosted on an HDD if there is any way to avoid it. An external USB drive would have slow file operations to and from that drive; an internal HDD would slow the entire system.

 5·5 months ago
5·5 months agoThere is an IOS app for hot air balloon pilots called “Hot Air”. There is a similar app for Android that… Leaves much to be desired.
There’s several functions that are needed. First, we need a map. We need to be able to enter waypoints and/or polygons charting landing zones, prohibited zones, targets, etc. we need an easy way to select targets, and our bearing and distance to those targets.
For planning purposes, we need a bearing line that we can place and move on that map. We need to be able to easily drag and drop each end of the line, and get the bearing and distance between the endpoints.
Next, we need track recording. It should record a ground track during flight, preferably with altitude information, and notes about the flight.
Next, a wind map. The wind speed and direction varies considerably by altitude. It needs to record direction and speed as we climb and descend, telling us what altitude has winds favorable for our current target.
Bonus points if we can prepopulate that wind map with data from a “pibal” (pilot balloon; a simple latex party balloon released and tracked with compass and stopwatch before a flight)
Next, coordination with other pilots and ground crews. 3D location sharing between participants; wind map data shared between pilots.

 125·5 months ago
125·5 months agoI’m not a fan of this approach. I think the idea that users should never touch a command line is an inherently proprietary philosophy. Without the command line, at any given moment, the user is fundamentally limited to whatever options the developer elected to offer.
I think a good GUI will assist a user in learning text configuration and command line functions.

 3·6 months ago
3·6 months ago“Hey, developer, your software is just about perfect for my use case, I just need to make this one small change. Can I go ahead and do that?”
"Sure, you can make that change, just as soon as you pay us $X. Oh, and we are planning on including that feature in the next release, so you can go ahead and buy that from us.

 2·7 months ago
2·7 months agoVPN server and any NAS or other network file share.
I got an email from the devs asking for style advice.

 4·11 months ago
4·11 months agoI remember when system memory was measured in KB…
Fuck, I’m old.
I haven’t found a program that gives me problems when I run it in a VM, but I haven’t run Photoshop in it, and I only spool up my Windows VM a couple times a year.
Last time was to run some janky-ass software to program an oddball Chinese UHF radio that was unsupported by Chirp.
Setup a Windows virtual machine inside your Linux environment. Now you’re not leaving Linux to get into your Windows environment.


My advice: Don’t setup dual boot.
Instead, setup Virtualbox in your Linux instance, and install Windows in a VM. You’ll have access to a windows “crutch”, without having to leave Linux to use it.